Security awareness topics for MSPs: risk-based list
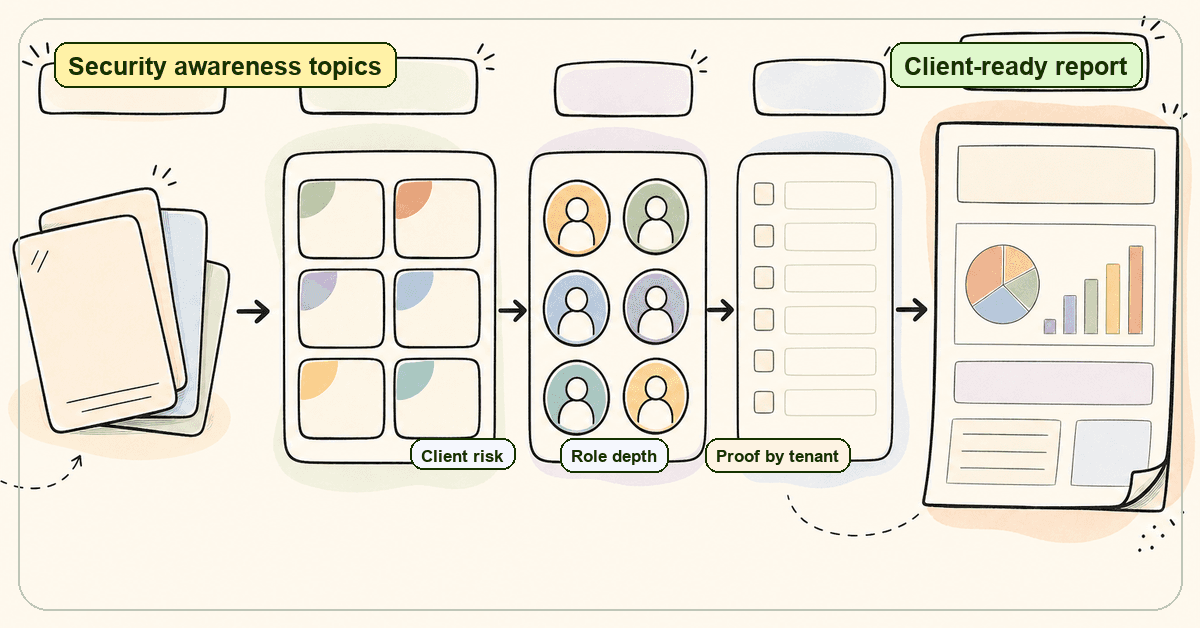
Security awareness topics for MSPs mapped to client risk, role, reporting, and compliance evidence without extra admin.
DefendWise
DefendWise
TL;DR
Security awareness topics are only useful when they are mapped to client risk, employee role, and proof.
A good MSP program does not need a giant annual content dump. It needs a repeatable topic set that covers phishing, reporting, BEC, passwords, MFA, software updates, data handling, AI-enabled scams, ransomware, and role-based responsibilities.
The operating problem is usually not "What should we teach?" It is "How do we keep the topics current, assign them by client, chase completion, and produce evidence without burning technician time?"
For MSPs, the best topic list is the one that can become a managed service: easy to assign, easy to report, and safe to scale across every client tenant.
What security awareness topics are
Security awareness topics are the recurring behaviours employees need to understand so they can work with security risk in mind.
NIST's Cybersecurity Framework describes Awareness and Training as personnel receiving cybersecurity awareness education so they can perform their information-security duties and responsibilities. In NIST CSF 2.0, PR.AT is focused on personnel having the knowledge and skills to perform general and role-specific tasks with cybersecurity risks in mind.
That wording matters. Awareness is not only a video library. It is a job-performance layer.
CISA's Secure Our World program reduces everyday security behaviour to plain actions: recognise and report phishing, use strong passwords and a password manager, turn on MFA, and update software. NIST's small-business phishing guidance makes the same practical move. It tells businesses to teach employees how to spot and report phishing, verify urgent requests through known channels, and use MFA, with phishing-resistant options for sensitive accounts.
For MSPs, the definition needs one more line:
Security awareness topics are the teachable behaviours an MSP can assign, repeat, and prove across multiple client tenants.
That last word, prove, is where most topic lists break.
Why generic security awareness topic lists fail MSPs
A generic list can be accurate and still fail the MSP.
It can name phishing, passwords, MFA, ransomware, privacy, and social engineering. Fine. But if every client receives the same calendar, the MSP inherits 3 problems.
First, the list does not reflect client risk. A law firm, a construction company, a school, and a healthcare provider do not have the same daily exposure. They share a baseline, but they do not share the same workflow, payment process, supplier pattern, or privacy obligation.
Second, the list does not create evidence. A client does not only need to hear that awareness happened. They need a clean answer when a board member, insurer, auditor, or executive asks who was trained, when, on what topic, and who is overdue.
Third, the list creates admin debt. Every topic becomes another assignment, reminder, export, client email, exception, and report. Multiply that by 20 clients and the content calendar becomes a support queue.
That is the MSP trap. The topic list looks like marketing. The work shows up in operations.
The security awareness topics MSPs should cover first
Start with the topics that connect to common loss paths, routine employee decisions, and evidence clients will ask for later.
| Security awareness topic | What employees need to practise | Who needs extra depth | Source signal |
|---|---|---|---|
| Phishing and message verification | Pause on urgent requests, inspect sender details, avoid unsafe links, and verify through known channels | Everyone, plus reception, finance, HR, and executives | CISA and NIST both treat phishing recognition and reporting as baseline behaviour |
| Reporting suspicious activity | Report suspected phishing, lost devices, account compromise, and mistakes early | Everyone | NIST small-business guidance tells companies to teach employees how to report suspected phishing |
| Business email compromise | Verify payment changes, payroll updates, executive requests, and supplier bank details out of band | Finance, payroll, executives, office managers | FBI IC3 reported more than $55 billion in exposed BEC losses from October 2013 to December 2023 |
| Password managers and unique passwords | Use long, unique passwords and avoid reuse across personal and work accounts | Everyone, especially users with client portals or finance access | CISA recommends password managers for long, random, unique passwords |
| MFA and phishing-resistant MFA | Turn on MFA, avoid approving unexpected prompts, and use stronger methods for sensitive accounts | Admins, finance, executives, healthcare, and high-privilege users | CISA says MFA makes users 99% less likely to be hacked; NIST recommends phishing-resistant authentication for sensitive apps and elevated roles |
| Software updates | Accept updates promptly and enable automatic updates where allowed | Everyone with laptops, phones, browsers, or remote-work tools | CISA tells users to install updates as soon as possible and turn on automatic updates |
| Safe data handling | Recognise sensitive information, avoid oversharing, use approved storage, and follow privacy handling rules | HR, finance, healthcare, legal, education, and client-facing teams | NIST CSF places data security under Protect, alongside awareness and training |
| AI-enabled scams and deepfakes | Verify voice, video, and urgent requests before sending money or data | Finance, executives, HR, and reception | FTC warns that scammers can use AI voice cloning and says to verify through known numbers |
| Ransomware and unsafe downloads | Avoid unknown attachments, report suspicious files, and understand why backups and updates matter | Everyone, with extra depth for admins | FTC phishing guidance notes phishing can install malicious code or ransomware |
| Role-based responsibility | Understand what the role must do differently: admin access, payment approval, data handling, incident routing | Admins, executives, finance, HR, IT-adjacent users | NIST SP 800-50 Rev. 1 includes role-based learning in its cybersecurity and privacy learning program scope |
This is a starter map, not a forever syllabus.
The point is to make the first 8 to 12 topics work hard. If a topic does not change behaviour, support a policy, reduce a real client risk, or produce useful evidence, it should not be high on the list.
How MSPs should map security awareness topics to client risk
A managed topic program needs a small amount of upfront thinking so it does not create weekly admin later.
Use 4 filters.
1. Client workflow
Ask where money, credentials, and sensitive data move.
A client that changes supplier bank details by email needs BEC and payment-verification training early. A client with field staff needs mobile-device, credential, and reporting topics. A client with regulated data needs data-handling reminders written in plain operational language.
Do not start with a vendor's content catalogue. Start with the client's day.
2. Role exposure
Everyone needs phishing, passwords, MFA, reporting, updates, and basic data handling.
Some roles need more. Finance needs payment-change verification. HR needs payroll-change and personal-data training. Executives need impersonation and out-of-band verification. Admins need MFA, privileged access, and incident routing.
The topic is the same. The risk story changes by role.
3. Evidence need
If a client asks for proof, what will you show?
A useful program should be able to answer:
- Which topics were assigned?
- Which users completed them?
- Who is overdue?
- Which roles received extra coverage?
- What reminders were sent?
- Which tenant does the evidence belong to?
This is why multi-tenant reporting matters. One spreadsheet across all clients is not MSP evidence. It is a sorting problem.
4. Service packaging
A topic list must fit the managed service you sell.
If every client requires manual topic selection, manual reminders, manual exports, and a custom monthly deck, the offer gets harder to deliver as it wins more clients. That pressure shows up as margin leakage, slow reporting, and awkward client exceptions.
The better pattern is a baseline calendar with light client overlays: standard topics for everyone, extra depth for exposed roles, and branded reports by tenant.
Step-by-step: build a 90-day security awareness topic plan
A 90-day plan is long enough to create movement and short enough to run without a planning committee.
1. Set the baseline topics
Pick the topics every client receives: phishing, reporting, passwords, MFA, software updates, safe data handling, and ransomware basics.
This creates a shared managed-service baseline. It also gives your team one repeatable operating model instead of 30 disconnected client calendars.
2. Add role-based overlays
Add BEC for finance and payroll. Add impersonation and AI-enabled scam verification for executives and assistants. Add privacy and data-handling depth for HR, healthcare, legal, and client-service teams.
NIST's awareness category is not limited to general users. It includes responsibilities aligned to duties, policies, and agreements. That is a strong argument for role-based topic coverage.
3. Decide the campaign cadence
Use short campaigns more often instead of one annual block.
A simple cadence works: 1 primary topic per month, short refreshers between campaigns, and quarterly client reporting. That gives clients progress without turning the MSP team into course administrators.
4. Write the verification rule
For each risky workflow, write the behaviour you expect.
For BEC, the rule might be: payment-detail changes must be verified by phone using a known number, not the number in the request. For AI voice cloning, the rule might be: urgent money or credential requests require a second channel and a known contact path.
The FTC's AI voice-cloning advice is blunt: do not trust the voice, call the person through a number you know is theirs.
5. Assign by tenant and role
Do not manage every client from a shared bucket.
Assign training by tenant, then by role inside the tenant. That keeps reporting clean and makes it easier to see which client needs follow-up.
This is where multi-tenant security awareness training matters for MSPs. The operational win is not fancy hierarchy. It is clean separation, cleaner reporting, and fewer manual mistakes.
6. Automate reminders before technicians get involved
The MSP team should not be the reminder engine.
Use automated nudges for overdue users, then escalate only the exceptions that matter. If a platform cannot handle basic assignment and reminder flow, the topic plan will land back in tickets and inboxes.
For MSPs trying to reduce admin, automation around onboarding, assignments, and reminders is part of the product requirement, not a nice extra.
7. Report the topic story, not only completions
A completion percentage is useful, but it is thin by itself.
The client needs the story: which topics were covered, why those topics matter, which roles received extra depth, who is overdue, and what the MSP recommends next.
That is why automated client-ready reports matter. They turn the topic program into a QBR asset instead of a spreadsheet chase.
What good security awareness topic coverage looks like
Good coverage is not a longer content library.
Good coverage has 7 traits:
- Baseline plus role depth. Every user gets the basics, and exposed roles get extra coverage.
- Client-specific risk mapping. The MSP can explain why each topic matters for that client.
- Tenant-separated evidence. Reports do not mix users, clients, or completion records.
- Clear reporting pathways. Employees know how to report phishing, suspected compromise, lost devices, and mistakes.
- Out-of-band verification habits. Finance and leadership teams know when to verify through a second channel.
- Regular refreshers. Topics appear throughout the year, not only during an annual compliance push.
- MSP-scale workflow. Assignments, reminders, and reports do not depend on one technician remembering every exception.
The last point is the one buyers often miss.
A client may judge the program by the training content. The MSP feels the program through the admin load.
Security awareness topics to avoid treating as generic modules
Some topics are too tied to workflow to be treated as generic learning.
Business email compromise
BEC training should not be a generic "spot the scam" module.
FBI IC3 describes BEC as a sophisticated scam that targets businesses and individuals who perform legitimate fund transfers. The same PSA says BEC was reported in all 50 US states and 186 countries, with more than $55 billion in exposed losses from October 2013 to December 2023.
That topic needs a workflow rule. Who can approve a supplier bank change? What channel verifies it? What happens if the request comes from the CEO? What if the voice sounds real?
MFA
MFA training should not stop at "turn it on."
CISA says MFA is a layered approach requiring 2 or more credentials, and that using MFA makes accounts 99% less likely to be hacked. NIST adds an important qualifier: some MFA methods can be phished, and sensitive apps or elevated roles should consider phishing-resistant authentication.
Teach the behaviour, not only the setting. Users need to know not to approve unexpected prompts, not to share one-time codes, and when to ask for help.
AI-enabled scams
AI scam awareness should not become a panic module.
The FTC gives a practical example: a scammer can use a short audio clip and a voice-cloning program to sound like someone the victim knows. The advice is simple enough to train: do not trust the voice, verify through a known number or another trusted channel.
For MSP clients, this belongs with BEC, executive impersonation, payroll change requests, and urgent payment approvals.
Data handling
Data handling should not be a legal lecture.
Employees need to know what data is sensitive, where it may be stored, when it may be shared, what tools are approved, and who to ask when unsure. That includes AI tools. If employees paste client data into unapproved tools, the problem is partly awareness and partly policy clarity.
Framework mapping for security awareness topics
Frameworks do not usually tell an MSP exactly which monthly topic to run. They tell the MSP what evidence the program should support.
| Framework or source | What it says | MSP evidence to keep |
|---|---|---|
| NIST CSF PR.AT | Personnel and partners receive cybersecurity awareness education aligned to duties and responsibilities | Assigned topics, completion records, role-based coverage, policy alignment |
| NIST CSF 2.0 PR.AT-01 and PR.AT-02 | General personnel and specialised roles need knowledge and skills to perform tasks with cybersecurity risk in mind | Baseline training plus role-specific topic assignments |
| NIST SP 800-50 Rev. 1 | Cybersecurity and privacy learning programs include awareness, behaviour change, role-based learning, security culture, and privacy culture | Program plan, campaign calendar, learner records, role mapping |
| CISA Secure Our World | Users should report phishing, use strong passwords and MFA, and update software | Topic coverage for phishing, passwords, MFA, and updates |
| FTC small-business phishing guidance | Staff should take 5, verify through known contact details, keep systems patched, and prepare response steps | Phishing training, verification rules, incident routing, response reference material |
This is the reporting opportunity for MSPs.
Do not tell clients, "We trained your staff." Tell them, "Here is the topic coverage tied to the risks we manage for you, and here is the evidence by tenant."
How Defendwise fits
Defendwise is built for MSPs that need security awareness training to work as a managed service.
Flat pricing at $399/month removes the per-seat pressure from training coverage. White-label delivery keeps the MSP brand in front of the client. Multi-tenant structure keeps clients separated. AI-native content support helps MSPs keep topic coverage relevant without rebuilding the calendar by hand.
If you are comparing the operating model, look at flat-fee pricing, white-label delivery, and compliance reporting together. The topic list is only half the job. The MSP workflow is the other half.
Frequently asked questions
What are the most important security awareness topics for employees?
The most important security awareness topics for employees are phishing, reporting suspicious messages, password managers, MFA, safe software updates, data handling, BEC, AI-enabled scams, and incident reporting.
MSPs should add role-based topics for finance, executives, admins, HR, and users who handle sensitive client data.
How many security awareness topics should an MSP include in a program?
Start with 8 to 12 recurring topics.
A huge one-time library can look impressive, but it often creates poor retention and weak reporting. A smaller topic set mapped to risk, role, and evidence is easier to run and easier to explain to clients.
How often should security awareness topics be refreshed?
Refresh topics throughout the year.
Quarterly campaigns, short monthly reminders, and role-based updates are easier to absorb than one annual block. They also give the MSP more chances to report progress.
What topics should finance teams receive?
Finance teams should receive BEC, supplier bank-change verification, payroll-change verification, executive impersonation, MFA, password manager, phishing, and AI-enabled voice or video scam training.
The behaviour to train is verification before action, especially when money or account details change.
What security awareness topics support compliance evidence?
Phishing, reporting, MFA, passwords, data handling, role-based responsibility, acceptable use, and incident routing can all support compliance evidence.
The evidence needs to show assignment, completion, overdue users, reminders, topic scope, and tenant separation.
Should MSPs use the same security awareness topics for every client?
Use the same baseline, but not the same emphasis.
Every client needs phishing, passwords, MFA, reporting, and updates. Finance-heavy clients need more BEC work. Regulated clients need stronger data-handling and privacy reminders. Admin-heavy clients need privileged-access depth.
How does Defendwise help MSPs manage security awareness topics?
Defendwise gives MSPs flat-rate, white-label security awareness training for unlimited users and clients at $399/month.
That makes broad topic coverage easier to package because the MSP is not punished with a new vendor seat bill every time a client adds users.
Source notes
External sources used for this article:
- CISA, Recognize and Report Phishing: https://www.cisa.gov/secure-our-world/recognize-and-report-phishing
- CISA, Use Strong Passwords: https://www.cisa.gov/secure-our-world/use-strong-passwords
- CISA, Update Software: https://www.cisa.gov/secure-our-world/update-software
- CISA, Secure Our World resources: https://www.cisa.gov/resources-tools/resources/secure-our-world-cybersecurity-awareness-month-resources
- CISA, Multifactor Authentication: https://www.cisa.gov/topics/cybersecurity-best-practices/multifactor-authentication
- NIST, Protect function and Awareness and Training: https://www.nist.gov/cyberframework/protect
- NIST, CSF 2.0 PR.AT summary: https://csf.tools/reference/nist-cybersecurity-framework/v2-0/pr/pr-at/
- NIST, Small Business Cybersecurity: Phishing: https://www.nist.gov/itl/smallbusinesscyber/guidance-topic/phishing
- NIST, Small Business Cybersecurity: MFA: https://www.nist.gov/itl/smallbusinesscyber/guidance-topic/multi-factor-authentication
- NIST SP 800-50 Rev. 1, Building a Cybersecurity and Privacy Learning Program: https://csrc.nist.gov/pubs/sp/800/50/r1/final
- FTC, Cybersecurity for small business: Phishing: https://www.ftc.gov/business-guidance/blog/2018/11/cybersecurity-small-business-phishing
- FTC, Scammers use AI to enhance their family emergency schemes: https://consumer.ftc.gov/consumer-alerts/2023/03/scammers-use-ai-enhance-their-family-emergency-schemes
- FBI IC3, Business Email Compromise: The $55 Billion Scam: https://www.ic3.gov/PSA/2024/PSA240911
- Microsoft, What is Business Email Compromise?: https://www.microsoft.com/en-us/security/business/security-101/what-is-business-email-compromise-bec
- Verizon DBIR overview: https://www.verizon.com/business/resources/reports/dbir/
Internal links used in this article: